|
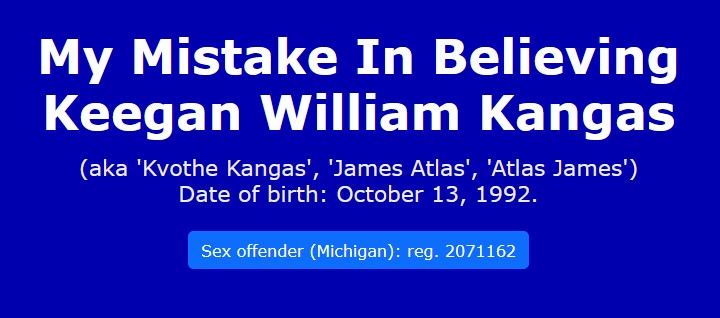
When I spoke with Kangas on 12 May (2017), and I told him that I had been viewing his old Facebook messages
that corroborated what the two 13-year old girls had said about him having sex with them (and what the prosecution had asserted), he was clearly
alarmed and the only 'solution' he offered me was that the messages were fake. He said that it was possible to alter the date of Facebook
messages, and the MI prosecution must have written all the incriminating messages in anticipation of the appeal that he intended to make: I
viewed this to be yet another of his ill-conceived 'smokescreens' that he failed to recognize could be easily refuted or invalidated. It
seems that when he is confronted with a problem of his own making, he chooses to lie, and then, when something written by him turns out to be
damaging, he simply claims that "someone else wrote it", and seems unconcerned about the ridiculous features that the proposal will
require. While dates can be amended, there are several major problems with his denial of the authorship of the Facebook messages. Firstly, (i)they were mentioned in his trial so if the 'fake' ones had existed at that time, the defence would have raised an objection (as you will read in the following, it is possible to determine if a message is 'fake'); (ii)if however, these 'fake' messages were written after the trial, in anticipation of an appeal, then again, it would be possible to show they are 'fake', not only by the IP address used (as discussed below), but also by comparing them with those that were held by the defence at the trial. He commented that he gave his Facebook login details to his attorney and she shared the same building with the prosecution, i.e., intimating that the prosecution burgled her office and somehow obtained the login details: the prosecution then accessed the account and spent many hours, or days or perhaps even weeks, forging countless messages to implicate Kangas in the crime: and yes, Kangas was being serious. For simplicity, from hereon, I shall refer to the person, who supposedly did all of this according to Kangas, as 'Mr X'. This enterprise would not be limited to simply forging messages from Kangas's account and backdating them as Kangas not only sent incriminating messages but he received replies to these as well, so Mr X would have had to access the accounts of those people who replied to Kangas, e.g., the two 13-year old girls, meaning that Mr X would have had to write/post the girls' replies to Kangas's account, with an accompanying forged date, i.e., ensuring they were given backdated time-stamps to 'appear' during the relevant period when the prosecution said Kangas committed the crimes (November 2012 to January 2013). But now the problems really begin. Even if Mr X was not only able to gain access to Kangas's Facebook account, but the accounts of the two 13-year old girls also, and this allowed him to reply to Kangas's messages (which of course would have been actually written and given 'backdated' datestamps by Mr X), with backdated messages from the girls' accounts, there remains a question of how he also achieved this with Kangas's acquaintances, who also discussed his relationship with the two girls, but would have been unwilling to assist the prosecution. But let's say for sake of argument, that, somehow, Mr X managed to access their accounts too, and sent 'backdated' replies to Kangas (or Kangas's account), why did none of these people question why these strange messages were suddenly appearing on their own accounts as 'sent' messages? There is of course the very major question of why any rational, sane person would do all of this, and risk prosecution and a lengthy imprisonment for 'planting false evidence' for a crime such as CSC3? Particularly if they were a law enforcement officer or someone employed in the MI legal profession. It could be argued that, as a very last resort, a law enforcement agency/agent might consider undertaking such activity if Kangas were a dangerous terrorist or a serial killer, but the suggestion that all of this would be done, with the risk of a lengthy term of imprisonment for doing so, to convict a foolish 20-year old, is absurd, particularly as the prosecution already had numerous witnesses to testify against him at the trial (whereas there were none for Kangas's defence). By this stage it becomes obvious that Kangas was unaware of what is involved in internet/Facebook usage and the presence of the 'IP address', which is essentially a 'digital fingerprint', i.e.,
Internet activity is accompanied by an IP address. In Wikipedia we read:
In sum, activity that involves or includes sending Facebook messages will be accompanied by an IP address (it is possible to create another address by using a proxy server, Tor or an anonymizer (and recently a VPN service), but this would not assist Mr X as it would still not provide an IP address that coincided with the date on a 'fake' backdated message, nor would it agree with internet activity (or inactivity) on Kangas's account, or from his location or telephone line. If anything, it would create further doubt as most of these facilities often use IP addresses outside the US, e.g., Asia, Africa, South America, etc.) The following sample extracts below show that even if Mr X wrote 'backdated' messages from Kangas's account to incriminate Kangas, and somehow, almost miraculously, was also able to send replies to these from Kangas's friends (who, as I say, would not co-operate with such activity anyway and would also have to be silent about all these backdated messages suddenly appearing on their accounts), there remains the salient factor that the IP address would show the messages were not written when the datestamp said they were, and that Kangas was not the author. The following statements from various articles testify to the fact that logs are kept of Facebook activity (e.g., messages sent and received) which would mean that if Kangas wished to challenge the authorship or authenticity of those messages on his old Facebook account, the IP addresses used could be ascertained and it would be possible to determine whether the addresses conflicted with the stated date/time and the location that Kangas used to access the internet, etc. A message genuinely posted by Kangas, and dated as say, 28 January 2013, would have an IP address of the same time and date as allocated by the ISP used by Kangas at his location/address and with his telephone line. However, if the IP address that appeared, did not coincide with the apparent usage, but say a year later, then it would be clear the message, albeit dated 28 January 2013 was a 'fake'. In the upshot, Kangas offers the 'fake message' scenario to explain the incriminating Facebook messages on his account, but 'fake messages' would be revealed as false as the IP address data would not agree with the message datestamps and could therefore be shown to be unrelated to Kangas. It is for that reason that no rational person would attempt to create 'fake' backdated messages as it would be a waste of time. In contrast, there can be no doubt that if the IP addresses for all of Kangas's incriminating messages were obtained and examined, they would agree with and show the time, ISP account, 'phone line and location that a genuine writing by Kangas would require. His argument therefore fails. Faced with the incriminating weight of the IP address, Kangas may of course offer some puerile argument, e.g., no one actually 'saw' him write the incriminating messages, but this is meaningless as child molesters always make sure there is no one around to witness their criminal behaviour - apart from the victim(s). The cold reality is that all the messages were written on his Facebook account on a computer/internet account that he used at an address in which he resided, and this is apart from the fact that the events related in his Facebook account all coincide exactly with his activites, movements and what is known of him and others knew of him. Therefore any attempt to extricate himself are worthless and must, inevitably, fail. NB. (a)The prosecution's questioning of one of the girls made specific reference to how she and Kangas messaged each other through Facebook, but no objection was raised about this by the defence attorney, nor was there any objection to (or even a mention of!) this in any subsequent appeal. In fact on 25 May 2013, K., one of his two victims, sent him a message, using her mother's Facebook account, saying; "People are saying i snitched, but i didn't. a detective came to me & asked to look through my messages with you & i said no.. he made me tho, i had no choice" (this was after the girl said that Kangas had 'sent people after' her.) (b)Kangas's denials of course follows his modus operandi, i.e., whenever he writes something that he later realises was a mistake, he backpedals and then claims that 'someone else did it', and also offers a far-fetched story to account for the event. Another example of this will be found in 'Examples of lies'. |
|
Information about Facebook and IP addresses: "Law enforcement officials can trace your IP address back to your exact physical address." http://www.cnet.com/ "Non-Public Access Records: By necessity, Facebook sees your IP address every time you connect. For security purposes it even keeps records of the IP addresses from which you've logged in. However, this is not information that Facebook makes public to its users. The only IP addresses Facebook users can track through Facebook communications are the ones for Facebook's own servers. Facebook can, however, reveal this information to law enforcement officials." http://itstillworks.com/ "Most of your Facebook data is available to you simply by logging into your account. For example, your Timeline contains posts you have shared on Facebook, along with comments and other interactions from people. Additionally, you can find your message and chat conversations by going to your inbox, or photos and videos you have added or been tagged in by going to those sections of your Timeline." https://www.facebook.com/help/ "Nearly a year on since Cambridge University researchers discovered that Facebook, along with other major social networks, doesn't erase server-side copies of your uploaded data, the world's biggest social network is still guilty of such a sin. Since then, the site has nearly doubled in size. It's now has the population of the third biggest country in the world, with tens of thousands of servers holding your data, which as soon as it is uploaded, belongs to them to do as and what they wish with it." http://www.zdnet.com/ "Facebook to release trolls' IP addresses. Nicola Brookes, 45, faced "vicious and depraved" abuse on Facebook...She took her case to the High Court in London where an order was granted last week compelling Facebook to reveal the IP addresses and other information of the people who had abused her." http://www.telegraph.co.uk/ "When I interviewed Facebook's director of security, Joe Sullivan, earlier this year, he told me the company provides only “basic subscriber information” in response to a subpoena, meaning a user’s name, e-mail address and IP address. Sullivan said that, to get a peek at a user's photos, status updates, private messages, friend lists, or pokes, law enforcement has to get a search warrant," https://www.forbes.com "First, the enforcement agency has to submit this form. In it they must give Facebook your email address, user ID or username. Once Facebook has the form submitted, they will then prepare an archive for the police to review. That archive will include the following. User ID number; Email address; Date and Time of your account’s creation; Most recent logins, usually the last 2-3 days; Your phone number, if you registered it; Profile contact info; Mini-feed; Status update history; Shares; Notes; Wall posts;Friends list; Groups list; Future and past events; Videos; Photos; Private messages; IP logs (computers and locations you logged in from). You’ll notice that this list includes just about everything that you’ve posted to Facebook. In addition, it also includes a list of your Friends, which you didn’t technically add to Facebook yourself." https://thenextweb.com/ "An IP address is a numerical address that is used for internet access the same way that a telephone number is used to access the public telephone network. When you connect to the internet your computer will always has an IP address associated with it in some way. However, the IP address rarely connected directly to a computer, but in fact is normally an address for a device between your computer and the internet, called a router. So the best you can do with an IP address is to find out the location and subscriber information for a router, not a specific computer. Why is this important? Knowing the address for a router can be of limited use for the following reasons...The router may be in a person’s home. If this is the case, then verification that the router is secured from unauthorized access can become an issue. If the router is in a person’s home, specifically the person who allegedly posted the evidence items on Facebook, then a subsequent subpoena to the internet provider is required to find this out by verifyng the subscriber information. Having the subscriber information would potentially show that the subscriber for the IP address at the time of the posting or account creation is the same as the person who made the posting. To do this you would need to perform the following steps in order 1.Get the Facebook ID for the account of interest. 2. Subpoena Facebook for activity logs to include the date, time and IP address information for a specific period of time. 3. Locate the IP address for the date and time of interest. 4. Locate the owner of the IP address, i.e. Time Warner, Comcast, etc. 5. Subpoena the owner of the IP address for the IP address for the specific date and time of interest to get the subscriber information." http://www.ncids.com/ ""Personal data is the 'oil' Facebook is drilling for," says Max Schrems, Austrian law student and founder of the advocacy group Europe versus Facebook. Facebook was, in Schrems' words, "dumb enough" to send him all his data in a 1,200-page PDF. It showed that Facebook kept records of every person who had ever poked him, all the IP addresses of machines he had used to access the site (as well as which other Facebook users had logged in on that machine), a full history of messages and chats and even his "last location", which appeared to use a combination of check-ins, data gathered from apps, IP addresses and geo-tagged uploads to work out where he was. As Schrems went through the document, he found items he thought he had deleted, such as messages, status updates and wall posts... All messages, including chat, you have ever sent or received. They can no longer be deleted and US agencies can access them at will..." http://www.wired.co.uk/ |
|
Supplementary The above refers to Kangas repeatedly denying involvement in the crimes for which he was convicted. However, pages appeared in 2021, apparently written by him, or on his behalf, that presented a different stance. Please see Supplementary - 2021 |